1Ai Answer (Ao2)
one from:
300 x 200
200 x 300
60,000
More help here -
300 x 200
200 x 300
60,000
More help here -
1aii answer (Ao1)
All colours are combinations of RGB
Each of R, G, B is 8 bits / 8 bits are allocated to the three primary colours red, green, blue
3 colours x 8 bits each = 24 bits
2 to the power of 24 colours can be represented
24 bits are used to represent the colour of each pixel
More help here -
Each of R, G, B is 8 bits / 8 bits are allocated to the three primary colours red, green, blue
3 colours x 8 bits each = 24 bits
2 to the power of 24 colours can be represented
24 bits are used to represent the colour of each pixel
More help here -
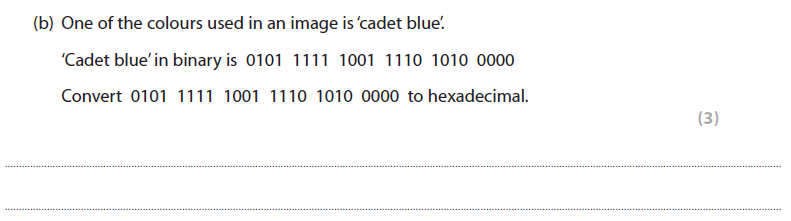
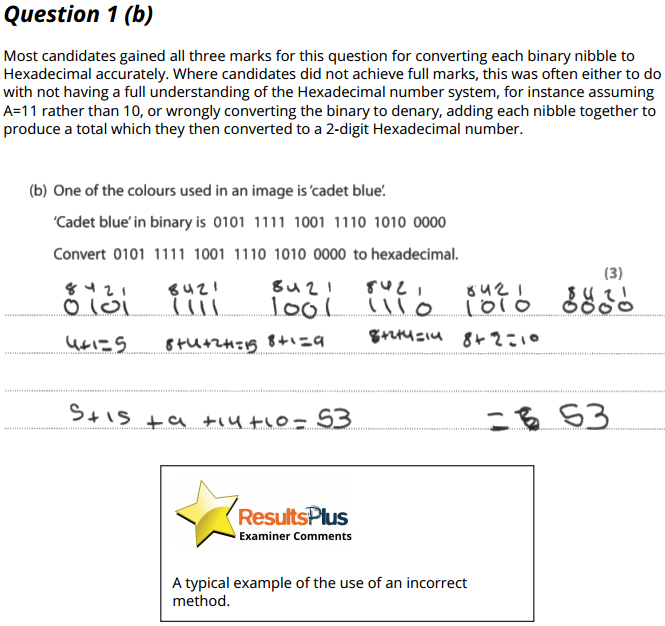
1b answer (Ao2)
5F 9E A0
More help here -
More help here -
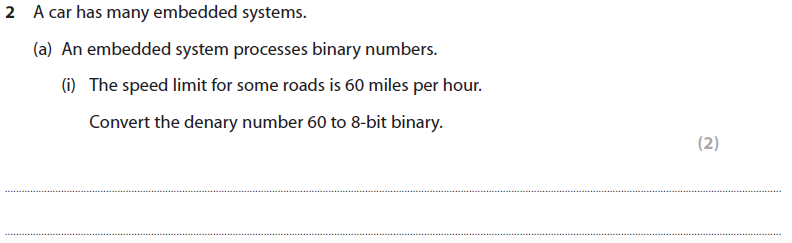
2ai answer (Ao2)
0011 1100
More help here -
More help here -
2aii answer (Ao2)
35
More help here -
More help here -
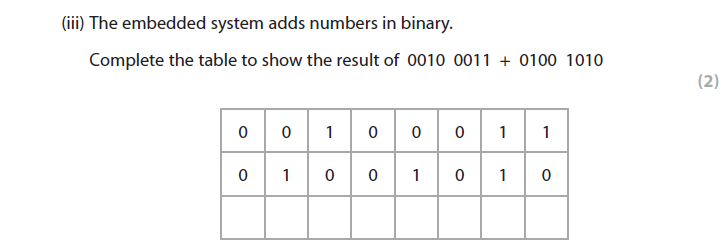
2aiii answer
0110 1101
More help here -
More help here -
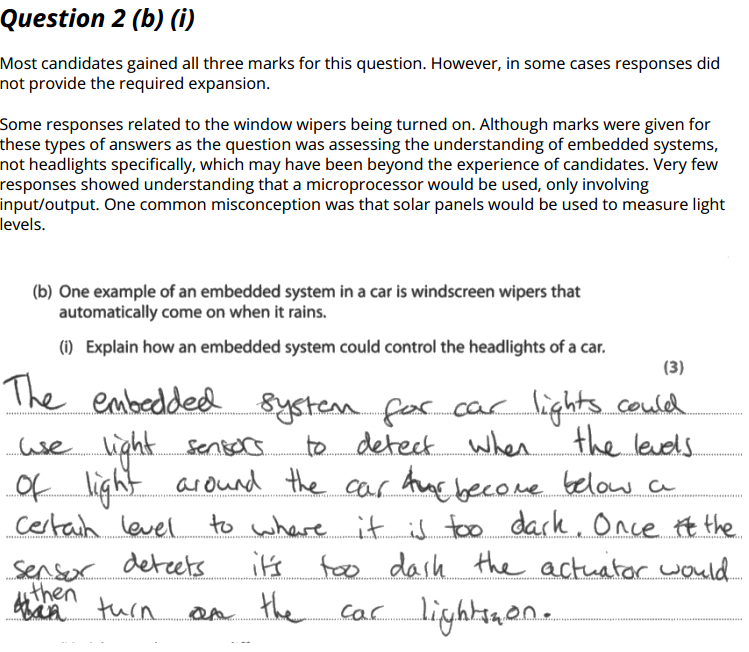
2Bi answer (Ao2)
A sensor (1) could be used with a microprocessor to determine light levels (1) to activate a switch / turn on/off the headlights
More help here -
More help here -
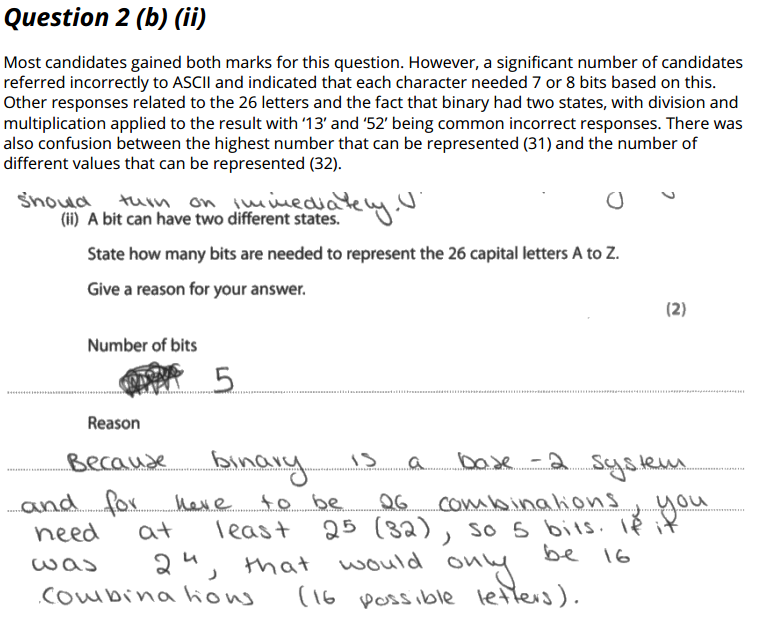
2bii answer (Ao2)
5 bits are needed
And one from:
because 4 bits / 2 to the power of 4 only represents 16 values
because 5 bits / 2 to the power of 5 represent up to 32 values
More help here -
And one from:
because 4 bits / 2 to the power of 4 only represents 16 values
because 5 bits / 2 to the power of 5 represent up to 32 values
More help here -
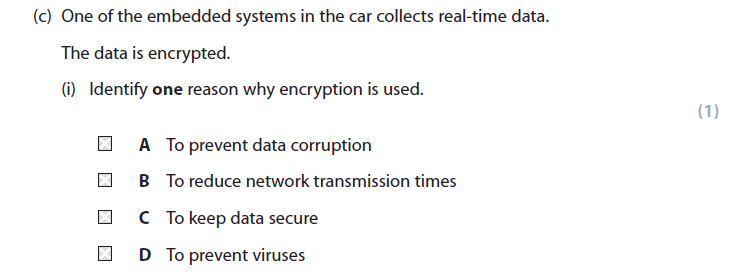
2ci answer (Ao1)
C - to keep data secure
More help here -
More help here -
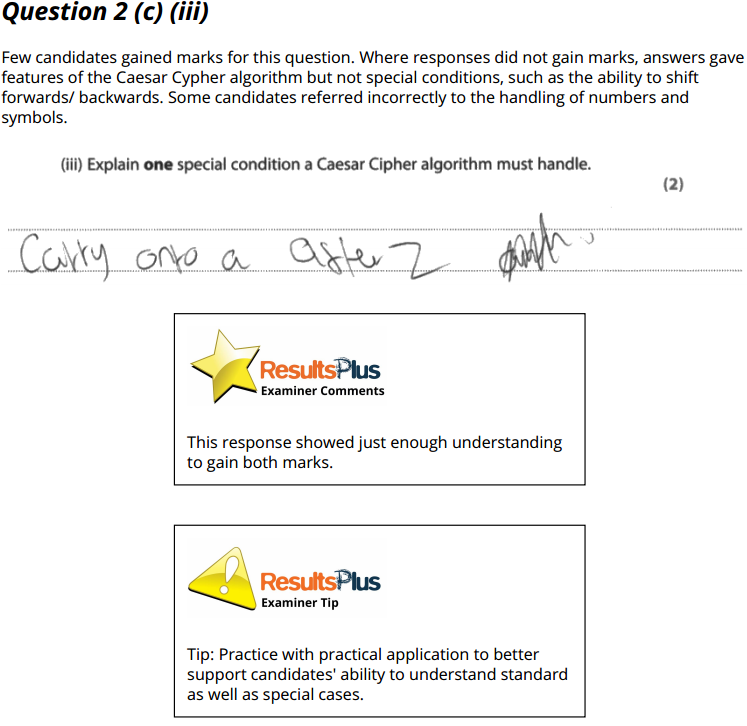
2ci EXAMINERS REPORT
No report
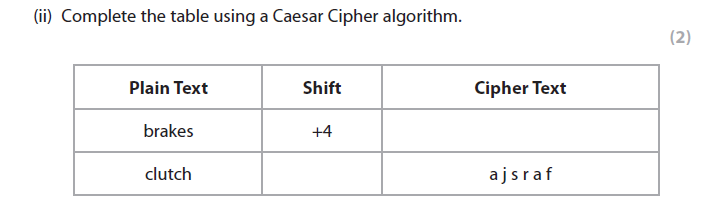
2cii answer (Ao1)
- f v e o i w
- -2
More help here -
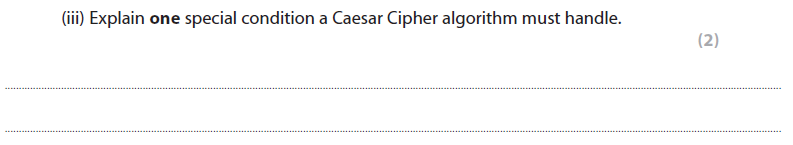
2ciii answer (Ao1)
When the start/end of the alphabet is reached (1) the algorithm must roll over (1)
More help here -
More help here -
3ai answer (Ao1)
Share peripherals/devices (e.g. printers, scanners) (1)
Communicate (e.g. email, instant messaging)
Share data
Deploy/Update applications
More help here -
Communicate (e.g. email, instant messaging)
Share data
Deploy/Update applications
More help here -
3aii answer (Ao1)
May not have space for cables to be installed
Employees and visitors can move around the building without disconnecting
Adding new users just means giving out the SSID password
More help here -
Employees and visitors can move around the building without disconnecting
Adding new users just means giving out the SSID password
More help here -
2BII Examiners report
3bi answer (Ao1)
Most people do not notice (1)
...because
People have a limited hearing range
OR
Sounds (frequencies/amplitudes) can be masked by other sounds
OR
People's brains will "fill in the blanks"
More help here -
...because
People have a limited hearing range
OR
Sounds (frequencies/amplitudes) can be masked by other sounds
OR
People's brains will "fill in the blanks"
More help here -
2BII Examiners report
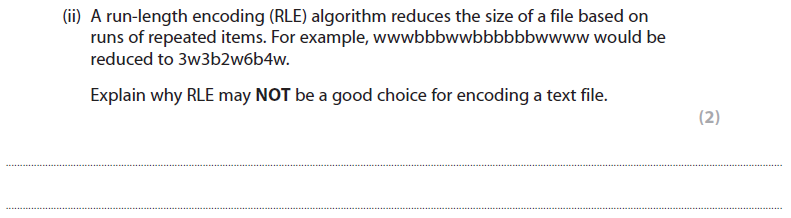
3bii answer (Ao1)
May increase the file size / the file may not be compressed very much / at all (1) if characters are distributed randomly/not repeated/runs of similar characters are found
More help here -
More help here -
2BII Examiners report
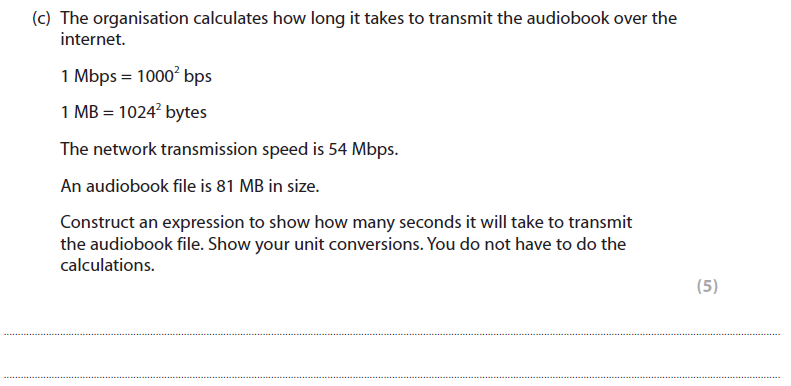
3c answer (Ao2)
Total number of bits to transfer
1 mark for 81 x 1024 o the power of 2
1 mark for x 8
Speed in bits per second:
1 mark for 54 x 1000 to the power of 2
Time = number of bits / bits per second:
81 x 1024 x 1024 x 8
-------------------------
54 x 1000 x 1000
1 mark = number of bits in numerator
1 mark = number of bits per second in denominator
More help here -
1 mark for 81 x 1024 o the power of 2
1 mark for x 8
Speed in bits per second:
1 mark for 54 x 1000 to the power of 2
Time = number of bits / bits per second:
81 x 1024 x 1024 x 8
-------------------------
54 x 1000 x 1000
1 mark = number of bits in numerator
1 mark = number of bits per second in denominator
More help here -
2BII Examiners report
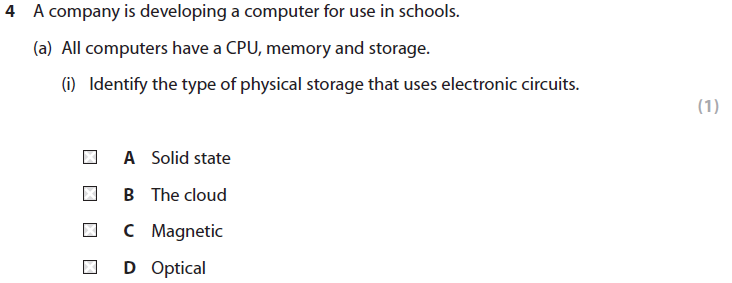
4ai answer (Ao1)
A - Solid state
More help here -
2BII Examiners report
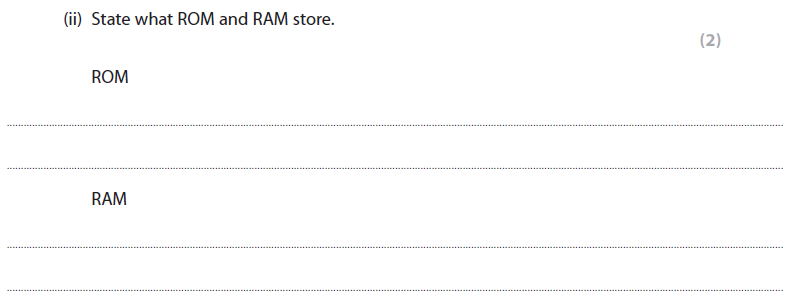
4aii answer (Ao1)
ROM stores BIOS / bootstrap / start-up (1)
RAM stores currently executing programs and data (1)
More help here -
RAM stores currently executing programs and data (1)
More help here -
2BII Examiners report
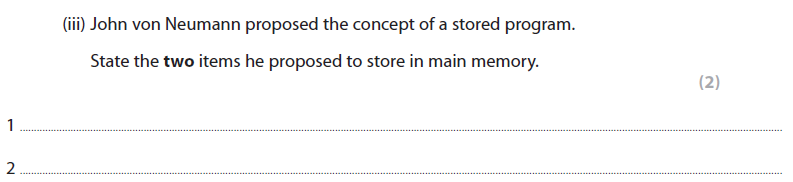
4aiii answer (Ao1)
Data
Instructions
More help here -
Instructions
More help here -
2BII Examiners report
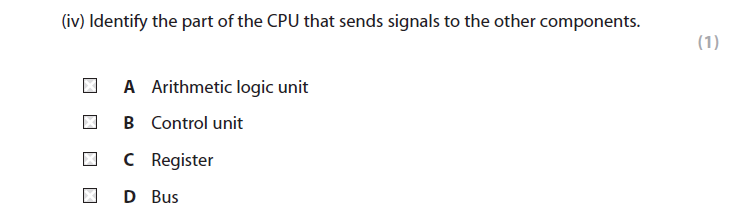
4aiv answer (Ao1)
B - Control unit
More help here -
More help here -
2BII Examiners report
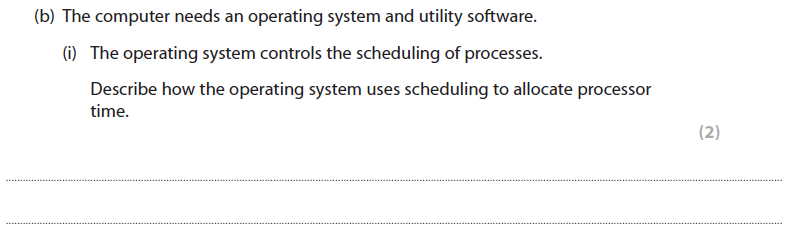
4bi answer (Ao1)
Any two from:
More help here -
- All processes are held in a queue
- Processes are prioritised
- (and) processes are switched
- On each clock cycle
More help here -
2BII Examiners report (Ao1)
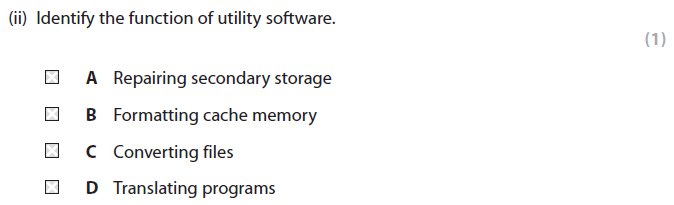
4bii answer (Ao1)
C - Converting files
More help here -
More help here -
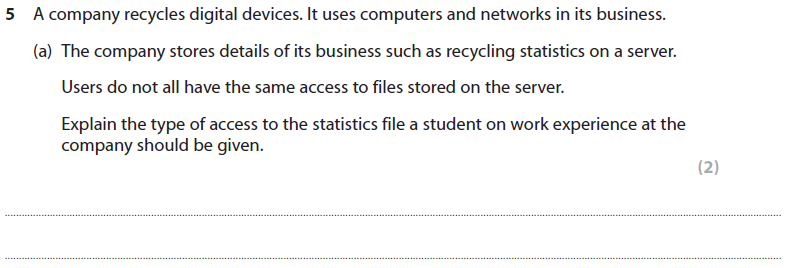
5a answer (Ao2)
An explanation that makes reference to one of these types of access:
More help here -
- Read only
- No access
- The student cannot see any sensitive/irrelevant information
- The student does not accidentally change/delete the data
- The student cannot share the data (outside the organisation)
More help here -
2BII Examiners report
2BII Examiners report
5b answer (Ao1)
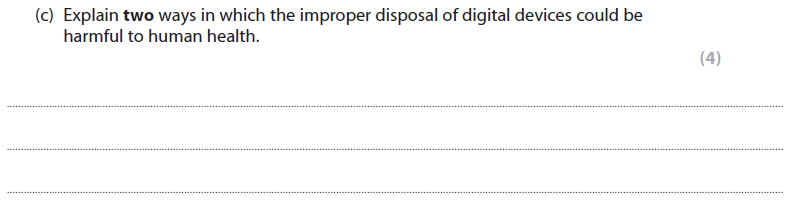
5c answer (Ao2)
- Disposal of digital devices in a landfill (1) could cause dangerous chemicals / toxins to leak (1) into drinking water (1)
- Reclaiming precious metals (1) exposes workers to more dangerous chemicals/materials (1) by contact during handling
- Incineration of digital devices (1) causes chemicals/toxins to be released into the air (1), which could then be inhaled (1)
- If batteries are not removed / thrown in a bin (1) they can catch fire (1) creating a risk of burns (1)
More help here -
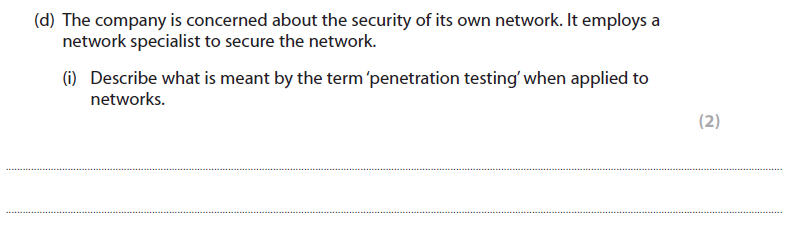
5di answer (Ao1)
Networks are put under deliberate attack (1) in order to identify any weaknesses/vulnerabilities (1) so that they can be fixed (1)
More help here -
More help here -
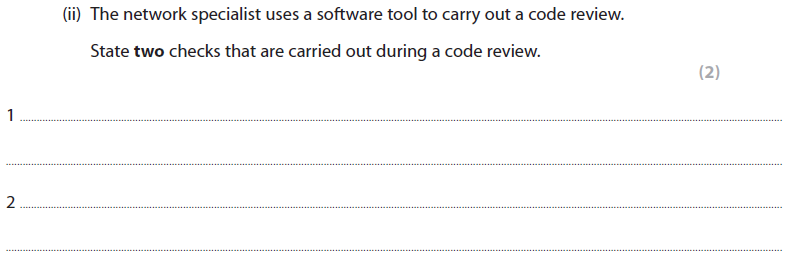
5dii answer (Ao1)
Any town from:
Identify:
More help here -
Identify:
- Bad programming practices
- inefficient code
- logic errors
- programming language-specific vulnerabilities
- security vulnerabilities
More help here -
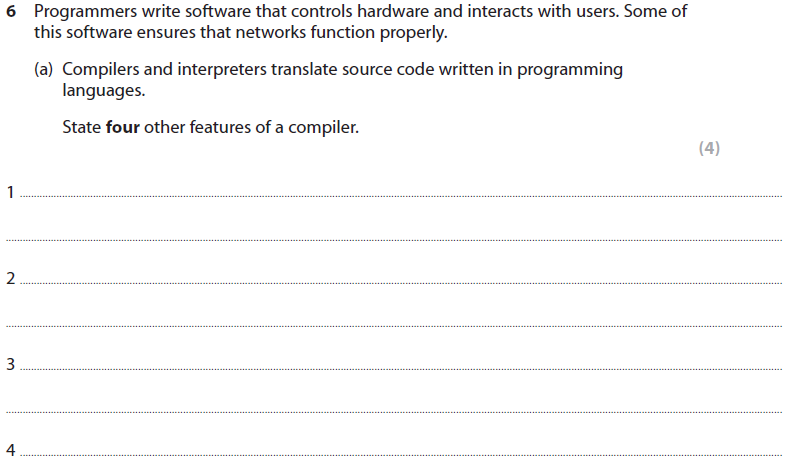
6a answer (Ao1)
Any four from:
More help here -
- A single executable file is produced
- The executable program is portable between machines
- The program source code is not available
- Code can be optimised/made more efficient
- Entire source code file is converted at once
- No special environment is needed to execute the code
- It creates object/machine code
- Error report s provided at the end of the compilation
More help here -
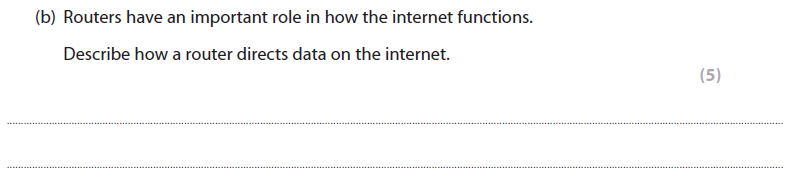
6B answer (Ao1)
A description to include five from:
More help here -
- Reads the data/packet to find the recipient's address
- Has physical connections to >=2 different networks
- Holds a routing table
- Stores information about (IP) addresses
- Keeps packets inside a network by not forwarding them
- Forwards data/directs/forwards/sends packets [Not directs data as in question]
- Chooses the mot efficient path to the next node
More help here -
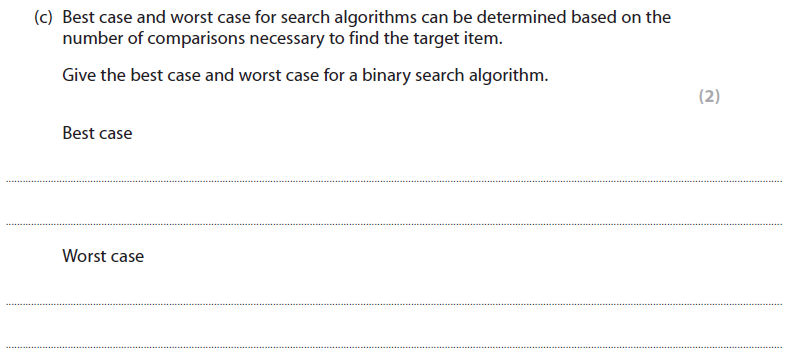
6c answer (Ao1)
Best case: the item is the middle / median of the list
Worst case: The item is not in the list / located at the point at which the final division could be made
More help here -
Worst case: The item is not in the list / located at the point at which the final division could be made
More help here -
6d answer (Ao2)
- All of the items appear to be stored on one single device
- The virtual device appears to be storage on the local machine
- Software sits between the physical devices and the user
- The items stored on the cloud could be scattered over several different physical hard discs/servers
- The items stored on the cloud could be resident in different locations
- Files need to be accessed via a network/internet
- Procedures (e.g. backup) happen without the end user being aware or involved
More help here -
Assessment Objectives occurrences in this exam
AO1 = 20 (Demonstrate knowledge and understanding of the key concepts and principles of computer science)
AO2 = 10 (Apply knowledge and understanding of key concepts and principles of computer science)
AO3 = 0 (Analyse problems in computational terms:
●to make reasoned judgements
●to design, program, evaluate and refine solutions.)
AO2 = 10 (Apply knowledge and understanding of key concepts and principles of computer science)
AO3 = 0 (Analyse problems in computational terms:
●to make reasoned judgements
●to design, program, evaluate and refine solutions.)